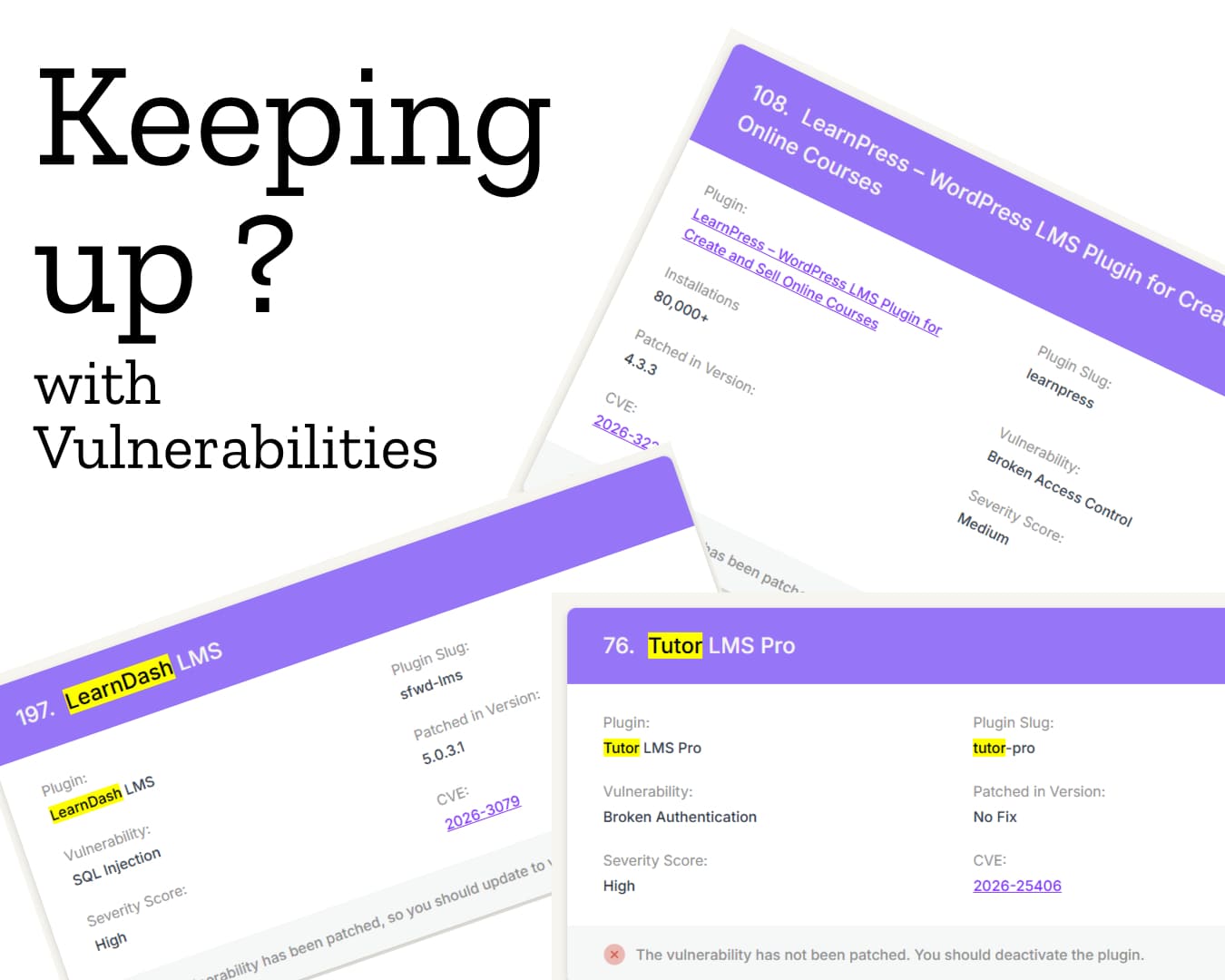
In 2025 alone, approximately 11,334 new vulnerabilities were reported across the WordPress ecosystem.
That translates to nearly 1,000 vulnerabilities every month.
For businesses and organizations that depend on WordPress, this is becoming an increasingly serious concern.
While WordPress recommends keeping websites regularly updated, the larger issue often lies beyond routine updates: zero-day vulnerabilities and delayed security patches.
A zero-day vulnerability is especially concerning because it becomes publicly known before a fix is available. In other cases, patches may be delayed because plugin or theme developers need time to investigate, develop, and release an update.
During that gap, websites remain exposed.
This is often the period when attacks happen.
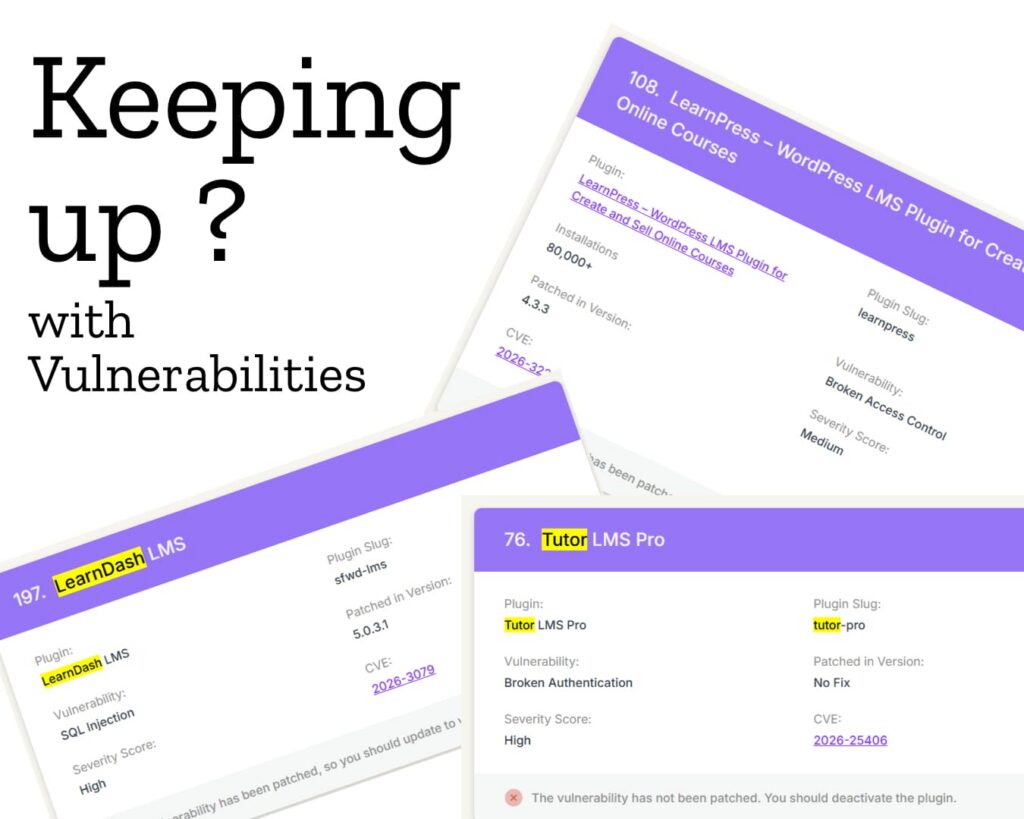
When Public Disclosure Becomes a Risk Multiplier
Once a vulnerability is published, the threat landscape changes immediately.
Many public reports include:
- technical details of the flaw
- affected versions
- proof-of-concept test code
- steps to reproduce the issue
While this level of transparency helps developers and security researchers, it also lowers the barrier for malicious actors.
Automated bots and organized attacker groups actively monitor these disclosures. I reported this in my article as back as 2021 by monitoring the server traffic we were getting specifically searching for some installed plugins.
Their systems can quickly:
- identify the affected plugin or theme
- scan the web for websites using it
- run automated proof-of-concept tests
- exploit vulnerable installations at scale
This makes the time between disclosure and patching extremely critical.
As I had previously discussed in my 2021 article on vulnerabilities arising from WordPress logged-in traffic, the risk often extends beyond the initial breach.
Once attackers gain access, they may leave behind persistent scripts, hidden admin users, or backdoors that allow them to return later.
This means that even after the visible issue appears resolved, the site may still remain compromised.
The Maintenance Burden on Businesses
This raises an important operational concern:
Can businesses realistically keep up with this scale of vulnerability exposure?
With thousands of new issues emerging every year, staying secure requires constant vigilance.
Most WordPress websites rely on multiple third-party plugins and themes.
Each dependency introduces another possible attack vector.
Security and maintenance timelines are often dependent on external developers, many of whom may be:
- under-resourced
- part-time maintainers
- small independent teams
- no longer actively supporting the plugin
Even paid plugins do not eliminate this concern entirely.
In many cases, businesses are paying recurring costs while still remaining dependent on third-party release cycles for critical security fixes.
A Broader Platform Stability Concern
This is no longer just a technical issue.
It is a broader concern around platform reliability, business continuity, and trust.
For site owners, the challenge is not only applying updates but also managing uncertainty around:
- zero-day vulnerabilities
- delayed patches
- abandoned plugins
- persistent backdoor risks
- escalating maintenance costs
The growing volume of disclosed vulnerabilities raises an important question for every business operating on an open plugin ecosystem:
How sustainable is this model in the long term?
0 responses on "A Growing Concern: The Rising Security Risk in the WordPress Ecosystem"